Something about this really fucks.
We can't find the internet
Attempting to reconnect
Something went wrong!
Hang in there while we get back on track
Something about this really fucks.
content note: physical illness, death, suicide.
one thing about spending enough time fearing death, for whatever reason and reasons that may be, is that one end to it is not removing the originator of that fear — which depending on your psyche or conditions may not always be possible — but learning to not fear death instead.
i basically think anyone who spends enough time in panic over enough years is liable to end up this way. the alternatives are burning to a husk, loss of reality checking, or suicide.
personally still a bit afraid — not so indifferent that i’d go hard for no reason when exercising yesterday, for instance, i give my body what it asks for (fluid movements, light effort, nothing anaerobic), but not so afraid that i won’t do my best to purposefully trigger the new arrhythmia when doing the holter monitor next week, despite risk inherent in inducing one.
i find i keep having to say to myself, if this is all it would take to kill me, then now or in two weeks accidentally say, it really makes no odds. that i have to deploy this regularly to move forward with my days evinces a certain something. and while the uncertainty itself is one degree of unbearable, a kind of assertion that i cannot trust in my self-knowledge, the collective absence of faith from others is another.
if the condition finally gets worse after decades, if everyone’s been telling you it’s false/“Just Anxiety”/psychosomatic/“functional” (given decades of panic disorder etc.), and now it’s enough to be visible, it’s a relief and starts to feel your only ally — the only true thing in all this time. i don’t know if it’s true that the same death i feared and felt daily in my mid-teens until my early 20s is this one, the one now manifesting so physically, or the one that stole a few years away from me from 2016, but on reflection i’ve spent most of the last 22 years actively fearing and feeling death.
an end to this uncertainty and the loneliness within it is not exactly an unwelcome thing in and of itself. we were never promised even one day of the beauty of life, y’know? and i have experienced so much of it, awe-inspiring and terrible and banal. nothing was ever ever promised.
Happy new year!
I guess I’m taking a slightly more laid-back approach to goals this year. Health issues have unfortunately progressed; whatever pain relief I was getting from the duloxetine (or otherwise), either that effect has worn off or the pain levels have risen to break through.
I’ve also encountered a new arrhythmia, so “sudden cardiac death” is back on the menu of dread. Holter monitor next week where I’ll try to reproduce that without dying. Rheumatologist follow-up appointment where I expect to be diagnosed with hEDS in … 12 weeks. So it goes.
Goals, then.
866 days now; the streak isn’t the important thing, but it has been a really good lesson in proving to myself I can stay consistent with things given the right motivation. (In this case, being able to speak my partner’s native language.)
Duolingo isn’t for everyone, and the course quality varies wildly, but the Spanish course for English speakers is incredible, and if you spend 15-20 minutes a day on it, and let it be your fallback activity when bored, you will steadily but surely gain an extremely real facility with the language.
(This much time is also enough to reliably sit around Obsidian/Diamond league, and sometimes it can be a nice dopamine hit to make an effort to finish at #1.)
I have the benefit of being around a native speaker all the time, but the first year or so my level wasn’t anywhere near being able to use it casually without it getting annoying for both of us. By now, we can switch in and out pretty comfortably around the topics I’ve covered lexicon for.
I’ve also added Portuguese on the side, spending roughly half my time each day on each, and it works pretty well! I wouldn’t start two at once (especially closely related languages like these; too confusing), but being a few years in with one makes it an easy way to bootstrap another habit. Português é estranho, mas eu gosto :) It’s a much shorter and less developed course than the Spanish one, so I expect I’ll finish it this year and start another in its stead.
Planning to slot this in with my Duolingo practice. I’ve been an on-and-off meditator for 20 years or so now. I need the equanimity now more than ever.
This has been a real struggle over the last year or two, with energy levels so low (and no microwave in the Tallinn apartment!), but since moving into my new place back in Melbourne it’s been a key focus. Just need to keep it up.
Charlotte’s been working non-stop on Ava BASIC (previously) since July, and hopefully we can get that into a complete MVP this year.
Having an “off” project would be nice. This is a vaguer goal, but I get the feeling technical writing would be a good fit for us.
So far I have an unsorted list of things I’d like to learn or improve at:
A follow-up to lottia notes:
Charlotte continues to write there (though about more topics now, including Nix and Git/jj), and I’m considering her readership bootstrapped after a year of crossposts. Her Atom feed is linked.
Cross-post from lottia notes.
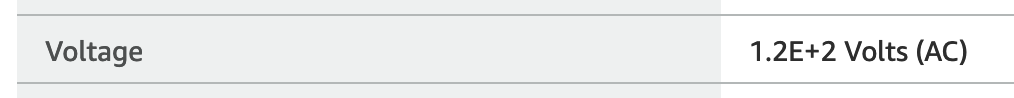 edit: Google tells me people hit this page a lot, searching for “1.2e+2 volts” and “what does 1.2e+2 volts mean”. It means 120 volts — it’s written in scientific notation (1.2 × 102), for absolutely no good reason.
edit: Google tells me people hit this page a lot, searching for “1.2e+2 volts” and “what does 1.2e+2 volts mean”. It means 120 volts — it’s written in scientific notation (1.2 × 102), for absolutely no good reason.
Cross-post from lottia notes.
Cross-post from lottia notes.
Cross-post from lottia notes.